Rise in Cybercrime
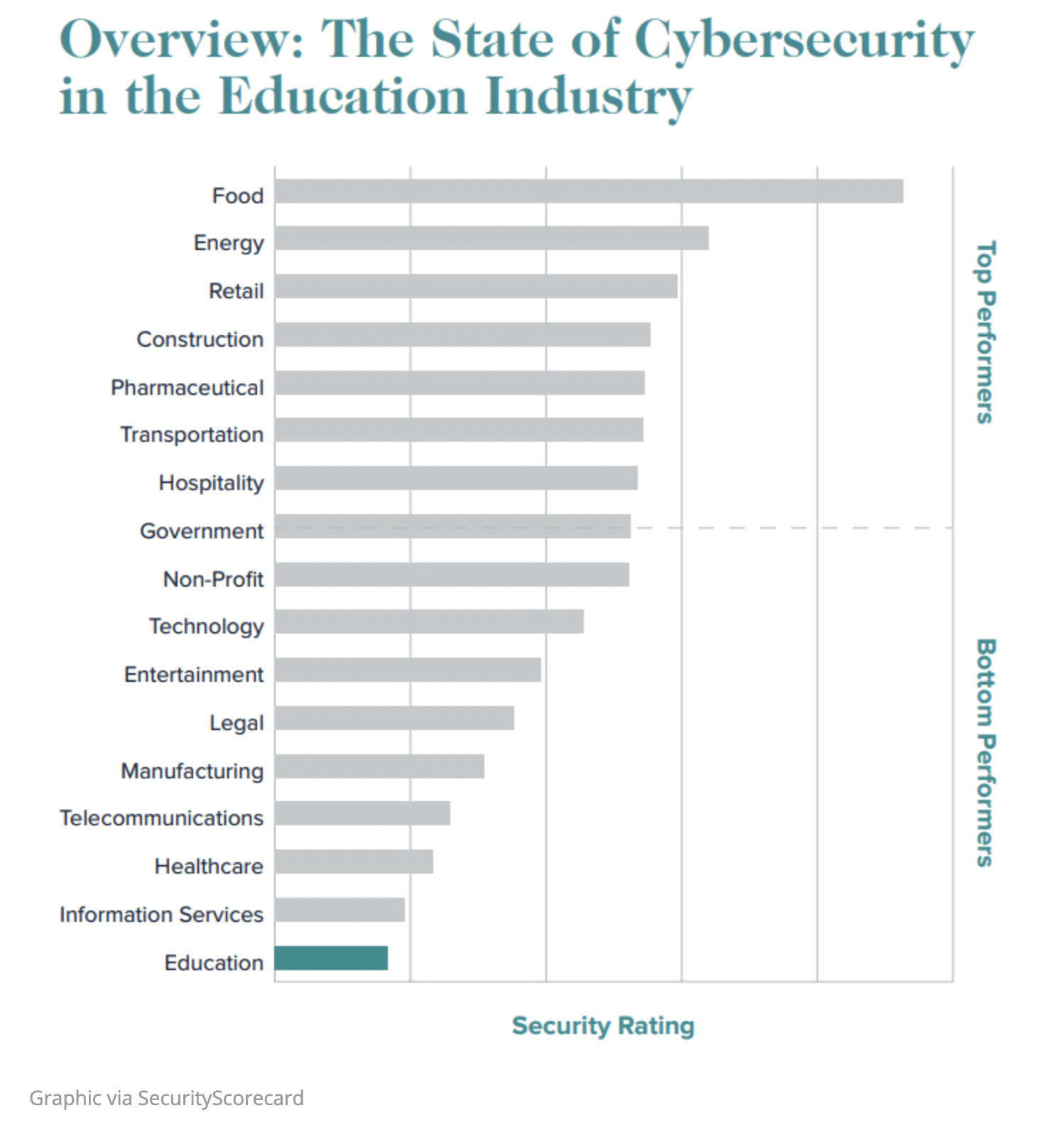
Higher education is an especially attractive target for cybercriminals because institutions possess large amounts of personal identifiable data, medical records, and advanced research project information. In fact, the education sector as a whole has recently been ranked the lowest performer in cybersecurity out of 17 industries. The most problematic vulnerabilities include application security, endpoint security, and patching software on a regular basis.
Also, according to Check Point Software, the average weekly attacks-per-organization in the education sector, from July-August 2020, increased by 30% when compared to the previous two months.
Impact
The financial impact of a cybersecurity incident is worth noting. A recent survey of institutions conducted by Campus Technology found that, of the institutions to have suffered a cybersecurity incident, the average cost spent for recovery was over $350,000. For a third of those institutions, it took a month or longer to find and remediate the issue.
Even more significant than the short-term financial loss to an institution from a cybersecurity incident is the violation of privacy and safety of its students and staff. (Of course, such an event could seriously damage a school’s reputation which, in turn, would have long-term effects.)
Let’s examine three cybersecurity trends that pose potential risks to higher education, along with some practical advice that institutions and users can apply to minimize those risks.
Increase in Phishing and Ransomware Attacks
There has been a drastic increase in phishing attacks and ransomware incidents over the past year. Cybercriminals are finding new ways to capitalize on the changing circumstances, with more people working remotely.
Phishing
Phishing is a form of social engineering attack. It has become one of today’s most common cybercrimes. In the broadest sense, phishing occurs when a cybercriminal uses a false identity to trick someone into providing sensitive information or to install malware.
Phishing schemes often use topical issues to entice users to download malicious files or click on nefarious links. For those in higher education, that might include offers of early access to COVID-19 vaccinations, access to approve a stimulus loan deposit to an institution’s bank, or other subjects that are both relevant to the user and have strong emotional influence.
Ransomware
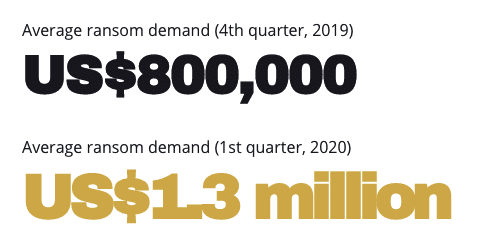
The purpose of many phishing schemes is to deliver ransomware. Ransomware is a form of malware where cybercriminals gain access to systems, encrypt crucial files on those devices, and hold the victim’s information at ransom. Bitdefender’s Mid-Year Threat Landscape Report 2020 states that there has been a 715% year-over-year increase in ransomware attacks. Additionally, the financial demand from these crimes has increased over 60%.
Trend Micro 2020 Midyear Cybersecurity Report
Evolving Attacks
These attacks usually start with a phishing email but can involve other means such as unsecured ports, file shares, or other remote services. More specifically, we’re seeing a rise in the use of fileless malware techniques.
Fileless malware is a type of malicious activity that uses native, legitimate tools built into a system to execute a cyberattack. Unlike traditional malware, fileless malware does not require an attacker to install any code on a target’s system. And it leaves no footprint, making it hard to detect. It leverages seemingly legitimate scripts or programs to execute malicious code while the programs continue to run. Moreover, many existing antivirus solutions today are unable to detect these types of attacks on systems.
Advice
While the industry is working towards finding solutions, we need to stay vigilant and adhere to security best practices. A few ideas to consider:
- Security awareness training is a key strategy used by security professionals to prevent and mitigate risks. These programs are designed to help staff and students understand that they play an important role in helping to combat phishing and ransomware attacks.
- From browsers to operating systems to enterprise applications, focus on getting software and systems up to date so vulnerabilities can be quickly patched. This includes keeping SaaS vendors accountable for making sure their solutions are addressing these new threats.
- Continuously monitor phishing emails and other incoming and outgoing network traffic.
Work from Home
With more staff working from home and students attending classes remotely, the areas prone to attack have increased exponentially. It’s inevitable that cybercriminals will start to compromise unsecured home networks to access systems and services on campus. The transition happened so quickly that most institutions did not have adequate time to fully consider the security implications of changes to the VPN configuration, remote desktop (RDP) access, or other common connections.
Change in Behavior and Devices
While working from home, users tend to be more prone to share their passwords with other people as a quicker way to get their tasks done. In a recent poll by SailPoint Technologies, 23% of respondents admitted to sharing their work passwords with a partner, roommate, or friend.
The scenarios and risks become magnified when these remote workers use personal devices (computers, mobile phones, tablets, etc.) and home internet connections for work/school purposes. Many times, these personal devices are not properly patched or configured. When one connects through a secure VPN, the campus network recognizes the computer as a trusted device. So, if the device is compromised, a malicious attacker or software could compromise other computers or servers on the campus network.
Advice
Some ways to mitigate these risks:
- Implement password management policies such as periodic password rotations and high password strength. Set clear rules around not sharing passwords. (This can also be a part of an overall security awareness training program within the institution.)
- Train users to be cautious when logging into unsecured networks such as public wi-fi connections. Additionally, users should ensure that their home wi-fi is secured using the latest wireless security protocols.
- Enforce multi-factor authentication on as many systems as possible, such as VPN connections.
- Review access levels and make sure they are correct or are still necessary. Often, access is granted to individuals to get a task done but then left in place because it is forgotten. A least-privileged model with time limits ensures that users have the minimal amount of access to get their work done.
More Interconnected Services and Infrastructure
Because of the pandemic, many universities’ IT strategies have shifted. In numerous cases, it accelerated their plans to move resources and systems to the cloud. This has resulted in a mesh of interconnected services comprised of both cloud and on-premise networks from various providers. This poses a risk if one of these components fails. Such a failure can lead to a partial or total outage. Don’t be surprised to hear about more of these incidents this year.
With the rush to the cloud, IT staff have been under tremendous pressure to migrate systems and keep business operations running. Simple best practices could easily get overlooked (Examples include accidently exposing network access controls or security groups; improperly encrypting data in-transit or at-rest; and not logging at different layers.)
More Than Just Technology is Needed
On a related note – but not an issue specific to higher education – there is a shortage of IT talent. The people who are knowledgeable in hosted solutions and cloud security best practices are in great demand, yet in short supply. A recent study conducted by the consulting firm Frost & Sullivan reveals that 70% of professionals globally believe there is a talent shortage. It will be important to train talent and collaborate with other security professionals to ensure these services meet the needs of the institution.
Advice
Some ways to address these issues:
- Incorporate vulnerability scans or penetration tests to root out potential security oversights.
- When in doubt, encrypt everything. Data should be encrypted both in-transit and at-rest. Make sure storage has encryption enabled and servers have valid SSL certificates.
- Establish a formal security policy that sets standards for staff and students’ digital activities.
- Modify and test the business continuity and disaster recovery plans with more automation. With complex integrations and data in several locations, automating failover for rapid restoration will be crucial.
Final Thoughts
Network and system security is never “finished.” Cybercriminals are tirelessly finding new and innovative ways to circumvent cybersecurity measures. Institutions must stay vigilant. If you haven’t already done so, now is the time to start a dialogue on cybersecurity at your institution. Don’t wait until a breach occurs!





0 Comments
0 Comments